Malware Removal Test 2016
| Release date | 2016-10-15 |
| Revision date | 2016-10-13 |
| Test Period | March - September 2016 |
| Number of Testcases | 45 |
| Online with cloud connectivity |  |
| Update allowed |  |
| False Alarm Test included |  |
| Platform/OS | Microsoft Windows |
| Methodology | Click here |
Introduction
Good malware detection is very important to find existing malware that is already on a system. However, a high protection or detection rate of a product does not necessarily mean that a product has good removal abilities. On the other hand, a product with low detection rate may not even find the infection and therefore not be able to remove it. Most AV vendors may by now already have addressed and fixed/improved the next releases of their products based on our findings in this report. Some users may wrongly assume that anti-virus products just delete binary files and do not fix anything else, e.g. the registry. This report is also intended as a little informational document to explain that professional anti-virus products do much more than just deleting malicious files. We advise users to make regular backups of their important data and to use e.g. imaging software.
For further details please refer to the methodology documents as well as the information provided on our website.
The test was performed from March to September 2016 under Microsoft Windows 10 64-Bit (English). Only products whose vendors subscribed to the 2016 public main test-series, and did opt-in for this test, are included in this report. In this test, the following 16 up-to-date Security Products were tested using 45 malware samples.
Tested Products
 ThreatTrack Vipre Internet Security Pro
ThreatTrack Vipre Internet Security Pro
Test Procedure
This test focuses only on the malware removal/cleaning capabilities, therefore all samples used were samples that the tested anti-virus products were able to detect. It has nothing to do with detection rates or protection capabilities. Of course, if an anti-virus is not able to detect the malware, it is also not able to remove it. The main question is if the products are able to successfully remove malware from an already infected system. The test report is aimed to typical home users and not administrators or advanced users who may have the knowledge for advanced/manual malware removal/repair procedures. Most often users come with infected PC’s with no (or outdated) AV-software to computer repair stores. The methodology used considers this situation: an already infected system that needs to be cleaned.
- Thorough malware analysis for each sample, to see exactly what changes are made
- Infect physical machine with one threat, reboot and make sure that threat is fully running
- Install and update the anti-virus product
- If not possible, reboot in safe mode; if safe mode is not possible and in case a rescue disk of the corresponding AV-Product is available, use it for a full system scan before installing
- Run thorough/full system scan and follow instructions of the anti-virus product to remove the malware, as a typical home-user would do
- Reboot machine
- Manual inspection/analysis of the system for malware removal and remnants
Malware Selection
The samples have been selected according to the following criteria:
- All security products must be able to detect the malware dropper used when inactive
- The sample must have been prevalent (according to metadata) and/or seen in the field on at least two PC’s of our local customers in 2016.
- The malware must be non-destructive (in other words, it should be possible for an anti-virus product to repair/clean the system without the need for replacing Windows system files etc.).
We randomly took and kept 45 malware samples from the pool of samples matching the above criteria.
Testcases
Below is a list of the used samples. Readers can ignore the IDs in parenthesis; we mention them only as a reference for the tested AV vendors to identify them based on the samples they received from us after this test. To avoid providing to malware authors information that could be potentially useful for them in improving their creations, this public report contains only general information about the malware/remnants, without any technical instructions/details.
| Sample 1 (636bb1): Ldpinch trojan | Sample 24 (5d8304): MultiInjector trojan |
| Sample 2 (bff91b): Nitol.B trojan | Sample 25 (cf0a6e): Slingup backdoor |
| Sample 3 (fce985): Noancooe backdoor | Sample 26 (966357): Ramnit virus |
| Sample 4 (6eaf78): DelfInject trojan | Sample 27 (e061a3): Cutwail trojan |
| Sample 5 (de2765): Crowti ransomware | Sample 28 (586b59): Dodiw backdoor |
| Sample 6 (f365f6): Banker trojan | Sample 29 (b9f08a): Sality virus |
| Sample 7 (76cbfa): Zbot trojan | Sample 30 (8c8470): Ainslot worm |
| Sample 8 (1f39ef): Phorpiex worm | Sample 31 (ea6f64): Gocok trojan |
| Sample 9 (056a11): Zegost backdoor | Sample 32 (5251c0): Banker trojan |
| Sample 10 (e25a35): Bladabindi backdoor | Sample 33 (17d9bb): Ursnif.B ransomware |
| Sample 11 (3a848e): Nitol.A trojan | Sample 34 (52e76c): Dorv.C trojan |
| Sample 12 (ab05af): CeeInject trojan | Sample 35 (cba22b): Gaertob backdoor |
| Sample 13 (c68610): Tescrypt ransomware | Sample 36 (00ab96): Sality.AU virus |
| Sample 14 (5b571e): NetWiredRC backdoor | Sample 37 (00c3f4): Gamarue worm |
| Sample 15 (e6ba41): Vobfus worm | Sample 38 (001d68): Fynloski backdoor |
| Sample 16 (1099ca): Fakon trojan | Sample 39 (0a912f): Kovter trojan |
| Sample 17 (169e15): Omaneat trojan | Sample 40 (0dafb4): Jenxcus worm |
| Sample 18 (845343): Latot trojan | Sample 41 (95666d): Weenloc ransomware |
| Sample 19 (085788): Ursnif trojan | Sample 42 (0ef29d): Renamer virus |
| Sample 20 (2e5639): Dorv.A trojan | Sample 43 (2b1f2e): Nuqel worm |
| Sample 21 (45c63a): IRCbot backdoor | Sample 44 (e42de1): HydraCrypt ransomware |
| Sample 22 (3d0f56): Bunitu trojan | Sample 45 (748b92): Dumpy worm |
| Sample 23 (449001): Dacic trojan |
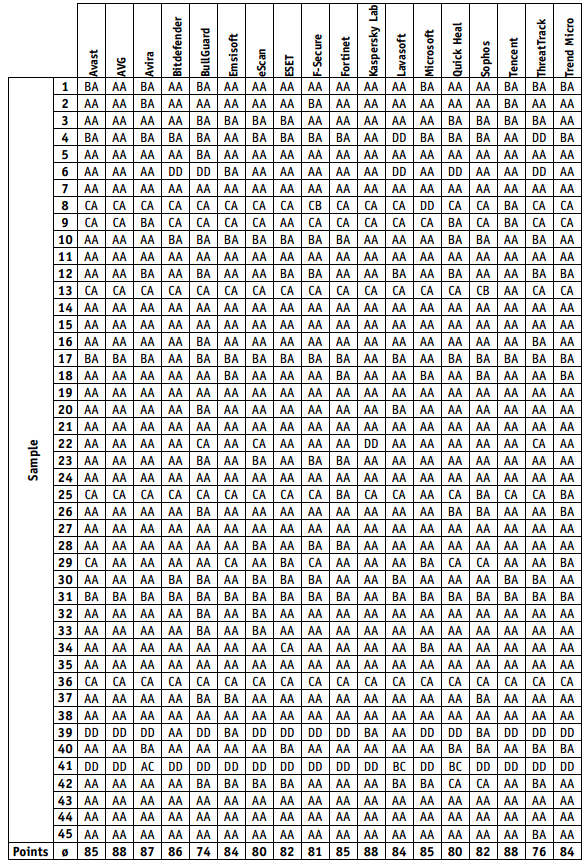
Ratings
We allowed certain negligible/unimportant traces to be left behind, mainly because a perfect score can’t be reached due to the behaviour/system-modifications made by some of the malware samples used. The “removal of malware” and “removal of remnants” are combined into one dimension and we took into consideration also the convenience. The ratings are given as follows:
a) Removal of malware/traces
- Malware removed, only negligible traces left (A)
- Malware removed, but some executable files, MBR and/or registry changes (e.g. loading points, etc.) remaining (B)
- Malware removed, but annoying or potentially dangerous problems (e.g. error messages, compromised hosts file, disabled task manager, disabled folder options, disabled registry editor, detection loop, etc.) remaining (C)
- Only the malware dropper has been neutralized and/or most other dropped malicious files/changes were not removed, or system is no longer normally usable; dropped malicious files are still on the system; removal failed (D)
b) Convenience
- Removal could be done in normal mode (A)
- Removal requires booting in Safe Mode or other built-in utilities and manual actions (B)
- Removal requires Rescue Disk (C)
- Removal or install requires contacting support or similar; removal failed (D)
Ranking System
| The following award/scoring system has been used | ||
| AA = 100 | AB = 90 | AC = 80 |
| BA = 70 | BB = 60 | BC = 50 |
| CA = 40 | CB = 30 | CC = 20 |
| DD = 0 | ||
| The awards are then given based on the rounded mean value reached | |
| ADVANCED+ | 86 – 100 points |
| ADVANCED | 71 – 85 points |
| STANDARD | 56 – 70 points |
| TESTED | lower than 56 points |
Test Results
Based on the above scoring system, we get the following summary results:
Additional Free Malware Removal Services
| Boot-Disk[1] available | Free Removal-Tools | |
| Avast | YES | – |
| AVG | YES | http://www.avg.com/eu-en/virus-removal |
| AVIRA | YES | http://www.avira.com/en/downloads#tools |
| Bitdefender | YES | http://www.bitdefender.com/free-virus-removal/ |
| BullGuard | – | – |
| Emsisoft | – | http://www.emsisoft.com/en/software/eek/ |
| eScan | YES | http://escanav.com/english/content/products/MWAV/escan_mwav.asp |
| ESET | YES | https://www.eset.com/int/download-utilities/ |
| F-Secure | YES | https://www.f-secure.com/en/web/labs_global/tools-beta |
| Fortinet | – | https://fortiguard.com/malwareremoval/ |
| Kaspersky Lab | YES | http://support.kaspersky.com/viruses/utility#kasperskyvirusremovaltool |
| Lavasoft | YES | – |
| Microsoft | YES | http://www.microsoft.com/security/scanner/en-us/default.aspx |
| Quick Heal | YES | – |
| Sophos | YES | https://www.sophos.com/en-us/products/free-tools/virus-removal-tool.aspx |
| Tencent | YES | – |
| ThreatTrack | – | http://www.vipreantivirus.com/live/ |
| Trend Micro | YES | https://esupport.trendmicro.com/en-us/home/pages/technical-support/1037161.aspx |
[1] Included in the standard package without extra charges (and without the need to contact/request it from the vendor’s support personnel).
The customer support of AV vendors may help the users in the malware removal process. In most cases, such support services are charged separately, but several vendors may provide their customers with malware removal help for free (i.e. service included in the charged product fee). We suggest that users with a valid license try contacting the AV vendor’s support service by email if they have problems in removing certain malware or issues while installing the product.
How some AV vendors could improve the help provided for home users with an infected system:
- provide/include a rescue disk in the product package (or provide links to download it)
- provide up-to-date offline-installers (e.g. if malware blocks access to the vendors website)
- do not require the user to login into accounts to install products or to activate the cleaning features (as malware could intercept passwords etc.)
- check for active malware before attempting installation
- point to standalone tools if installation fails or if malware could not be successfully removed
- include tools/features inside the product to fix/reset certain registry entries/system changes
- promote more prominently the availability of additional free malware-removal utilities provided, and free malware-removal procedures/support on the website, manuals, inside the product or when an active infection is found
Award levels reached in this Malware Removal Test
Copyright and Disclaimer
This publication is Copyright © 2016 by AV-Comparatives ®. Any use of the results, etc. in whole or in part, is ONLY permitted after the explicit written agreement of the management board of AV-Comparatives prior to any publication. AV-Comparatives and its testers cannot be held liable for any damage or loss, which might occur as result of, or in connection with, the use of the information provided in this paper. We take every possible care to ensure the correctness of the basic data, but a liability for the correctness of the test results cannot be taken by any representative of AV-Comparatives. We do not give any guarantee of the correctness, completeness, or suitability for a specific purpose of any of the information/content provided at any given time. No one else involved in creating, producing or delivering test results shall be liable for any indirect, special or consequential damage, or loss of profits, arising out of, or related to, the use or inability to use, the services provided by the website, test documents or any related data.
For more information about AV-Comparatives and the testing methodologies, please visit our website.
AV-Comparatives
(October 2016)