AV-Comparatives, an independent organization offering systematic testing of security software, is excited to announce its attendance and presentations at the RSA Conference in San Francisco in the first week of May. Continue reading…
Security News
On this page you will find links to selected IT-security related news articles from various sources, including news from conferences and some test results. Posts in this category might be written by externals and students. If you find some interesting news, please let us know!
AV-Comparatives Renews ISO 9001:2015 Certification for Independent Testing of Anti-Virus Software
AV-Comparatives is pleased to announce the renewal of its ISO 9001:2015 certification for the independent testing of anti-virus software. TÜV Austria has reaffirmed AV-Comparatives’ commitment to provide “Independent Tests of Anti-Virus Software” by extending the certification, validating the organization’s dedication to delivering high-quality evaluations in the field of IT security.
Updated AVC-News app for Android and iOS
AV-Comparatives is thrilled to announce the launch of the latest version of its AVC-News app, now available for both Android and iOS devices. The updated app offers users seamless access to the most recent news, test reports, and publications from AV-Comparatives, promising an enriched user experience and enhanced functionality across platforms
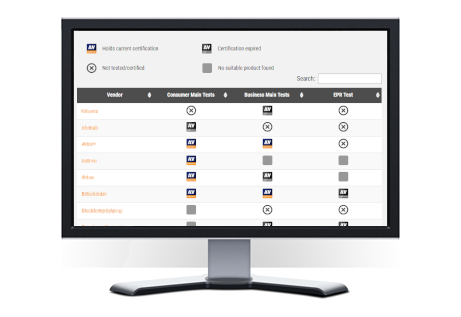
IT Security Products Overview
In response to the ever-evolving digital landscape, we’re excited to introduce the “IT Security Products Overview.” This compilation features 50 respected vendors, offering a practical guide for those looking to make informed decisions in the realm of cybersecurity. https://www.av-comparatives.org/security-products-overview/
Upcoming AV-Comparatives’ Certification Tests 2024
As in previous years, we will be running certification tests for the following products:
- Anti-malware programs for macOS
- Anti-malware apps for Android
- Phishing protection for Windows and other platforms
- Parental control features for Windows and other platforms
- VPN programs for Android and Windows
We also offer comprehensive security assessments exclusively for enterprise products, covering enterprise security tests, EPR/XDR tests, and penetration/red-teaming evaluations.
Security vendors interested in participating in any of the aforementioned tests or seeking more details are invited to contact us by 31st of March 2024.
Archive of AV-C Tests/Reviews 2004-2023
Explore AV-Comparatives’ Archive of Tests/Reviews spanning from 2004 to 2023 in PDF format below. For the latest evaluations, visit www.av-comparatives.org.
Please be aware that this list does not encompass all available tests on the website. Single Product Tests, specific Certification Tests, and reports not in PDF format are excluded. Additional reports can be found online here.
AVAR 2023: Reflecting on Cybersecurity Insights from Dubai
AV-Comparatives is delighted to share insights gleaned from the recent antivirus conference, AVAR 2023, held in the vibrant city of Dubai. The event, as predicted, delivered compelling discourses on IT security matters and provided an inclusive platform for both nationally and internationally recognised industry professionals to connect.
AV-Comparatives Hosts Successful Round Table to Foster Knowledge Exchange Between IT Security Vendors and Journalists.
AV-Comparatives, a leading independent testing organisation in the cybersecurity field, recently hosted a round table event focused on strengthening the knowledge transfer between IT security vendors and journalists.
AVAR 2023 Conference in Dubai
The AVAR 2023 Cybersecurity conference is taking place from 28th November till 2nd December.
The difference between AV-Comparatives’ EPR Test and MITRE ATT&CK Engenuity
Both the AV-Comparatives EPR Test and MITRE Engenuity have their merits, each providing useful insights into endpoint security solutions. Understanding the differences between these two tests is essential for IT managers, CISOs, and other tech-savvy professionals looking to select endpoint security solutions that will effectively protect their environments.